How to send WhatsApp Message without saving contact number on your...
How to send a WhatsApp chat without saving the contact
Now I show you how you can send WhatsApp Message without saving any contact number...
How to find that your smartphone has been hacked and How...
Smartphones are almost always connected to the internet, so it stands to reason that your phone hacked remotely. Hackers are always out there looking...
How to Install fonts on Kali Linux – Microsoft TrueType core...
Installing fonts is important for those who are multilingual or want to spice up their screen. Many websites use different fonts and without having...
How to install LazyKali and HackPack Script in Kali Linux
You learn Installing LazyKali and HackPack Script in Kali Linux. Also basic information about LazyKali and HackPack Script. This is a collection of scripts to add...
Different Types Of DDoS Attacks Used By Hackers
What is Distributed Denial of Service(DDoS) attack?
Distributed Denial of Services is a type of cyber attack that is mostly used by hackers to take...
Which operating system do ‘professional’ hackers use?
Which operating system do ‘real’ hackers use?
Which operating system do the ‘real’ hackers use? The real here is the cyber criminal type hackers and...
Skills Required to Become an Ethical Hacker
Skills allow you to achieve your desired goals within the available time and resources. As a hacker, you will need to develop skills that...
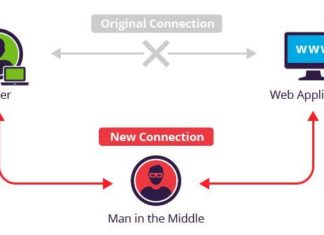
Man-in-the-Middle Tutorial: Learn About Man-in-the-Middle Attacks, perform man in the middle...
Man-in-the-Middle Attacks: ARP Poisoning
What is Man-in-the-Middle Attack?
In cryptography and computer security, a man-in-the-middle attack (MITM) is an attack where the attacker secretly relays and...